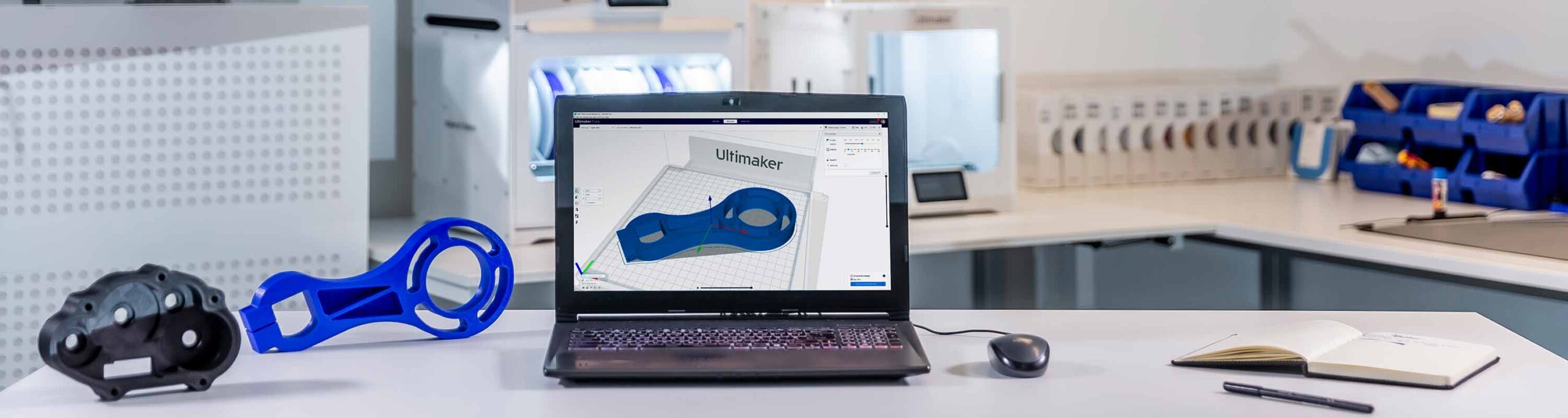
JUNE 23, 2022-- Ultimaker is delighted to announce we have achieved ISO/IEC 27001 certification – the leading internationally-recognized standard for information security management.
ISO/IEC 27001 certifies that the security policies Ultimaker applies across the organization – including all software and 3D printer products – are rigorous and robust.
Setting the standard
Achieving this gold standard makes Ultimaker one of the first 3D printing platforms on the market to be independently certified for security.
Jürgen von Hollen, CEO of Ultimaker, commented: “At a time when malicious cyber threats against organizations are on the rise, Ultimaker achieving ISO/IEC 27001 certification demonstrates our strong commitment to customer security. We understand that protecting information assets and avoiding costly disruption rank among the highest priorities for all organizations. That’s why Ultimaker has invested in implementing rigorous security procedures and protocols across its 3D printing platform, and why we factor security into every engineering decision we make.”
Our security commitment
While Ultimaker announces the certification today, our strong commitment to security is not new.
When developing and maintaining its products and services, we take all measures within our power to minimize and mitigate security threats that could impact customers. The key risks Ultimaker focuses on preventing are:
Loss of confidential information, such as print files or personal data
Business process interruption, especially due to threats that may target devices or applications as a stepping stone into customer systems and infrastructure
Any loss of quality during the 3D printing process
Infringement of customer data, products, and services
Ultimaker users can enable extra security features such as two-factor authentication and a 3D printer firewall
How we manage security
Maintaining this commitment involves applying rigorous, repeatable processes throughout software and firmware development, as well as creating product features that help users to stay secure. These include:
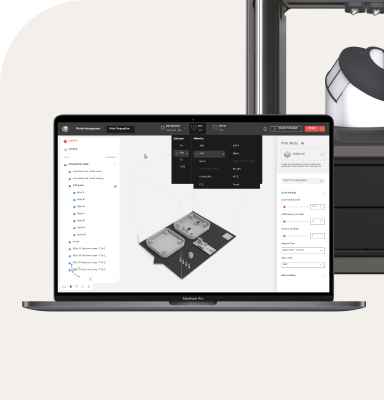
Data transmission and storage. Ultimaker services are designed in such a way that different data types about your print job are processed separately and independently. This means that customers can choose to only upload process data to the cloud while keeping product data on-premise. All cloud-based data, such as 3D files, G-code, and Ultimaker Marketplace source files, use HTTPS (TLS 1.2) connections with industry standard 2048-bit RSA encryption
Access controls. Ultimaker adopts the “principle of least privilege” through appropriate access control roles on a “need to know” basis. Sensitive information in our systems is redacted in application logging to ensure engineers can never access this information
Incident management and threat tracking. Ultimaker software teams regularly undertake education relating to the current information security landscape and have established processes for reporting, managing, and responding to incidents
Independent assessment. Products and services are assessed by third-party experts to validate our efforts to adequately mitigate privacy and security risks. Security assessments are conducted on a recurring basis, at least every six months
Customer choice. Different customers have different needs, which is why Ultimaker also offers various security features users can adopt, such as two-factor authentication and a 3D printer firewall
Continuous improvement. Ultimaker frequently releases updates to its software and 3D printer firmware to ensure the latest security principles are applied to all products and services – typically every two weeks in our cloud infrastructure and every two months for Ultimaker Cura
For sectors such as defense, aerospace, product development, research, and education, extraordinary levels of security compliance are often required. Ultimaker has longstanding relationships with customers in all these fields who have already demonstrated advanced security practices in their adoption of 3D printing.
With such protocols in place, even more organizations can benefit from a high security standard alongside the other benefits of Ultimaker’s additive manufacturing platform powered by the cloud – such as transitioning from costly physical inventories to a digital parts library, printing remotely across multiple locations, and enabling team members who could be using 3D printers for their work.
Want to know more about our security protocols and standards? You can read more about Ultimaker security practices, or the ISO/IEC 27001 standard. Or follow the link below if you want to know more about our leading 3D printing software platform.